1. Prerequisites
- Source Code in GitHub
- Spinnaker 1.16
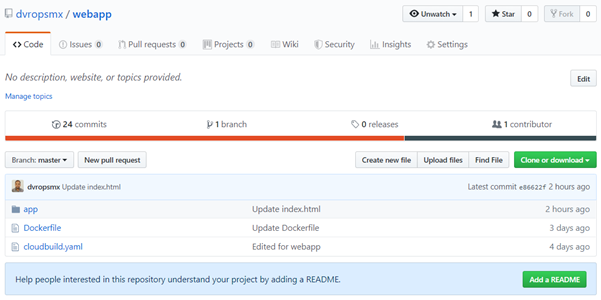
1.1 Source Code Repository in GitHub
Prepare a GitHub repository with some source code to build and it must contain either a Dockerfile or a cloudbuild.yaml file to configure the build.
1.2 Spinnaker
Spinnaker should be running with v1.16.1.
2. Google Cloud Platform (GCP) Configuration
2.1 GCP project
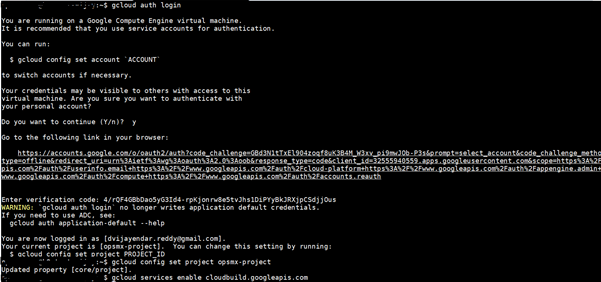
We need to have a Google Cloud Platform project with the Cloud Build API enabled. We can enable the API with the following gcloud command:
$ gcloud auth login
$ gcloud config set project opsmx-project
$ gcloud services enable cloudbuild.googleapis.com
2.2. Configuring Cloud Pub/Sub Notifications
When changes are made to the Container Registry repository, such as when images are pushed, tagged, or deleted, we can receive notifications using Cloud Pub/Sub.
Cloud Pub/Sub publishes messages about our repository to named resources called topics. These messages are received by applications subscribed to Cloud Pub/Sub topics. Subscriber applications send notifications when the repository’s state changes. Additionally, we can configure roles and permissions for our Cloud Pub/Sub topics to control how users interact with the repository.
$ PROJECT_ID=opsmx-project
$ SUBSCRIPTION_NAME=gcr-sub
Create a Cloud Pub/Sub Topic
A publisher application sends messages to the repository’s topic when the repository’s state changes. We can create a topic using either the GCP Console or the gcloud command-line tool.
create a new Pub/Sub topic
$ gcloud pubsub topics create gcr
Created topic [projects/opsmx-project/topics/gcr].
Create a Cloud Pub/Sub Subscription
Every Cloud Pub/Sub topic should have a subscription. A subscriber application receives messages from the repository’s topic.
# create a subscription for the topic
$ gcloud pubsub subscriptions create $SUBSCRIPTION_NAME --topic projects/$PROJECT_ID/topics/gcr --project=$PROJECT_ID
Created subscription [projects/opsmx-project/subscriptions/gcr-sub].
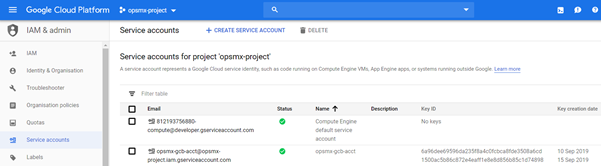
2.3. Setup IAM
We need to create a new service account for our project to authenticate Spinnaker with our GCP service account key file. A service account is a type of Google account that belongs to an application instead of a user, so we need one to authenticate our Spinnaker. Once again, we’re going to use Google Cloud SDK to help us with that.
PROJECT_ID=opsmx-project
SERVICE_ACCOUNT_NAME=opsmx-gcb-acct
# Create a new service account with lowercase letters, and consist of lowercase alphanumeric characters that can be separated by hyphens.
$ gcloud iam service-accounts create opsmx-gcb-acct
Created service account [opsmx-gcb-acct].
# Add the Pub/Sub Publisher role
$ gcloud projects add-iam-policy-binding ${PROJECT_ID} –member “serviceAccount:${SERVICE_ACCOUNT_NAME}@${PROJECT_ID}.iam.gserviceaccount.com” –role “roles/pubsub.publisher”
# Add the Pub/Sub Subscriber role
$ gcloud projects add-iam-policy-binding ${PROJECT_ID} –member “serviceAccount:${SERVICE_ACCOUNT_NAME}@${PROJECT_ID}.iam.gserviceaccount.com” –role “roles/pubsub.subscriber”
# Add the Pub/Sub Admin role
$ gcloud projects add-iam-policy-binding ${PROJECT_ID} –member “serviceAccount:${SERVICE_ACCOUNT_NAME}@${PROJECT_ID}.iam.gserviceaccount.com” –role “roles/pubsub.admin”
Add the Pub/Sub Editor role
$ gcloud projects add-iam-policy-binding ${PROJECT_ID} –member “serviceAccount:${SERVICE_ACCOUNT_NAME}@${PROJECT_ID}.iam.gserviceaccount.com” –role “roles/pubsub.editor”
Apart from the above roles, Add below two specific roles for Cloud Build:
- Cloud Build Service Account
- Cloud Build Editor
# Download a key file containing the credentials
$ gcloud iam service-accounts keys create ${SERVICE_ACCOUNT_NAME}.json --iam-account ${SERVICE_ACCOUNT_NAME}@${PROJECT_ID}.iam.gserviceaccount.com
created key [8f0bc1da68965b48c3364035f8611121ee57d379] of type [json] as [opsmx-gcb-acct.json] for [opsmx-gcb-acct@dvrs1-251908.iam.gserviceaccount.com]
We should have downloaded a .json file with the project’s credentials to the local machine.
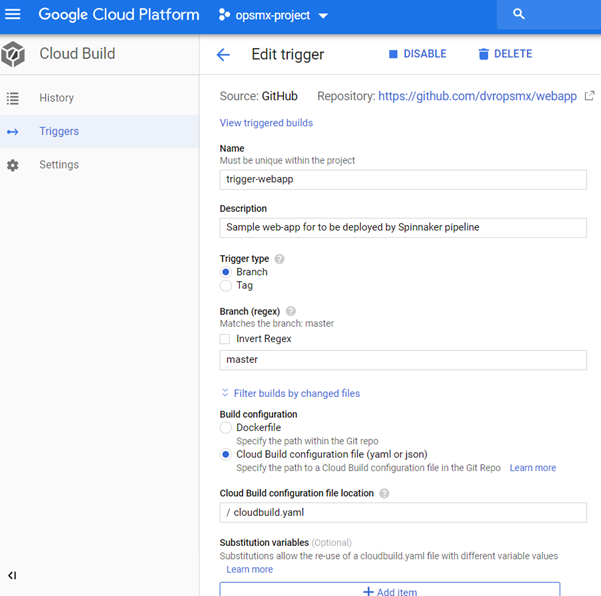
2.4. Setup Build Trigger
We are going to add a build trigger to initiate our pipeline. To do this, we have to navigate to Tools -> Cloud Build → Triggers. Here, click the button Add Trigger and we will be given a choice to select from either Github or Bitbucket.
Once we select our repository, we will be navigated to the build config page. Please fill the details as shown in the screenshot below and create the trigger.
Now everything is configured and we can do a Git push in the repository and the pipeline will jump to action.
3. Configure Spinnaker to listen to the Google Cloud Pub/Sub Subscription
3.1. Add the following entry to igor-local.yml file (in ~/.hal/default/profiles/)
locking:
enabled: true
3.2 Use the following Halyard commands to create a GCB account, enable the GCB integration, and re-deploy Spinnaker
$ hal config pubsub google enable
$ PROJECT_ID=opsmx-project
$ SUBSCRIPTION_NAME=gcr-sub
$ ALIAS_ACCOUNT_NAME=gcp-acct
$ SERVICE_ACCOUNT_KEY=/home/opsmxuser/dvrs/opsmx-gcb-acct.json
$ hal config ci gcb account add $ALIAS_ACCOUNT_NAME --project $PROJECT_ID --subscription-name $SUBSCRIPTION_NAME --json-key $SERVICE_ACCOUNT_KEY
$ hal config ci gcb enable
# login Docker with the below command
$ docker login -u _json_key -p "$(cat /home/opsmxuser/ opsmx-gcb-acct.json)" https://gcr.io
# Create a new file called, ‘.dockerconfigjson ‘ with the content of “auth” value from .docker/config.json file.
# Create a Secret based on existing Docker credentials
$ kubectl create secret generic regcred --from-file=.dockerconfigjson=/home/opsmxuser/.docker/config.json --type=kubernetes.io/dockerconfigjson
$ hal config provider docker-registry account add esw-docker-registry --address gcr.io --username _json_key --password-file /home/opsmxuser/ opsmx-gcb-acct.json
$ hal deploy apply
Later update this secret name ‘regcred’ for ‘imagePullSecrets’ in the deploy manifest file as shown in the below step #4.2
4. Configure Spinnaker Pipeline Trigger
Configure Spinnaker pipeline to be triggered by a completed GCB build.
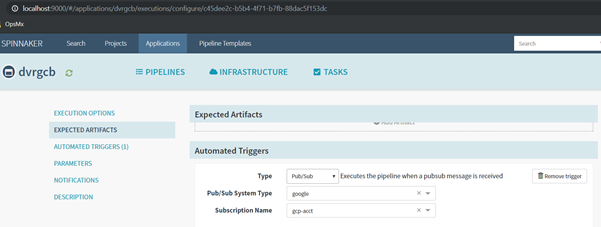
4.1 Configuration Stage
- In Pipeline configuration, click the Configuration stage on the far left of the pipeline diagram.
- Click Automated Triggers.
- In the Type field, select Pub/Sub.
- In the Pub/Sub System Type field, select google.
- In the Subscription Name field, select $ALIAS_ACCOUNT_NAME value.
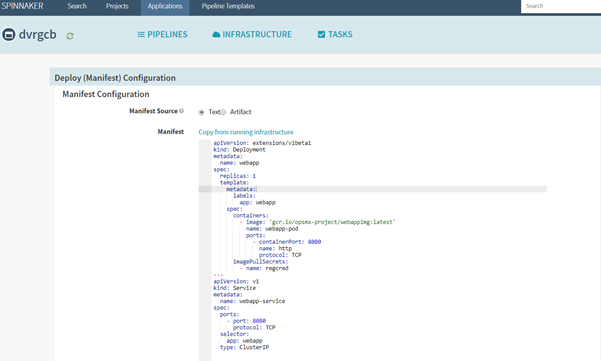
4.2. Deploy Kubernetes Manifests
Select the Deploy (Manifest) stage by specifying the manifests statistically.
Add manifest configuration to pull the webapp image (gcr.io/opsmx-project/webappimg) from Google Container Registry(GCR) and deploy it on configured Kubernetes cluster(my-k8-account).
5. Conclusion
1. Make a change into the repository (https://github.com/dvropsmx/webapp.git) for initiating the build to be auto triggered in Cloud Build.
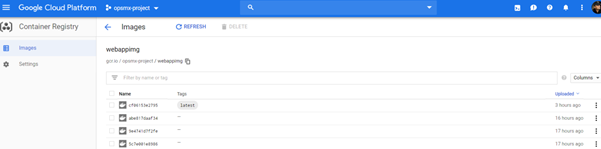
2. Ensure the resultant build is available in GCR as shown below:
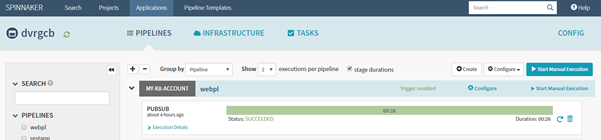
3. And the respective Pipeline in Spinnaker should be auto triggered by PUBSUB and Succeeded its execution as below:
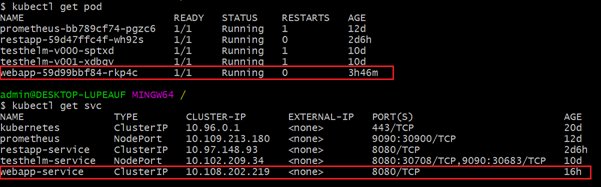
4. And see the subsequent result in kubernetes cluster as below:
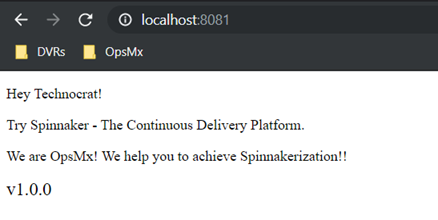
5. Check the sample webapp result in browser:

0 Comments